Gm Hackers !
In recent post, I presented to you what Operating Systems to use, Browsers and search engine. This time we're going into something that also pertains every internet user and namely the communication
{% embed https://dev.to/luftietheanonymous/privacy-and-security-setup-to-use-in-2026-part-1-os-browser-search-engines-53mc %}
If you did not read my last post, do it before reading that one, by clicking above
Over what channels/apps should you actually communicate anonymously ? This post will cover the essentials to start using more private tech. But before..., I have something relevant to announce
IMPORTANT ANNOUNCEMENT ⚠️
In September 2026, Google plans to officially block any app that does not belong to a developer, who do not have an account in Google Play Developer Console, haven't uploaded their ID there and paid a fee.

From someone who is kind of a normie guy, does not care about the tech, surrounding world and their only worry is about to be right on time to watch their movie in TV, it might sound as a rational argument, they want to prevent android from having malware/spyware/scam-apps on their systems, thus they require their ID and pay the fee for app deployment and demand the apps to be deployed only via Play Store.
Whereas on the other hand, Android natively with google is the biggest malware and spyware together with Microslop OS (known by Normies as Windows).
By default your Google Play Services have access to all your accessories in the phone like camera, microphone and location. So if you do not turn them off, there is more chance your data is gathered, misused and sold. In such way, you are controlled by the technology and not conversely.
Why it matters ?
The opportunity to build, launch your apps on android without needing to pay fees, load your ID to the Third-party company that is prone to frequent breaches and is has the worst products that could be ever given is exactly the normality the user and developer wants to have.
Developers can independently deploy their apps without needing to have any financial commitments or needing to identify themselves to a third-party company.

Think about programmers, youngster coders from African Countries (I have many friends from Nigeria (shout out to all my Nigerian brothers , you're phenomenal hard-workers. I love you all)). Do you think they will have enough money to purchase a subscription and simultaneously keep their life at the standard they have without any external support ?
I truly doubt it, of course for some it would be feasible, but I hear personally how those people are misused and paid slavery-salaries and try to handle somehow the money for another data packages (they do not have wi-fi, you white-trash morron ).
Another thing is that the app might not comply with often imaginary Google Play Requirements to push the app to be visible to the Store.
For now, indie mobile app devs simply can attach an .apk to their website/webapp and let users download from there, which is actually a common solution on the internet e.g. for games.
From the other perspective, it also is a violation of freedom of users of phones with custom ROMs like GrapheneOS or LineageOS, but also the average pure android user, that should decide themselves and take the risk on their own where they want to download their apps from, and it should not be estabilished by only-profit driven company, that is seeing the competition in solutions like FDroid and wants to have a monopoly.
When it comes to custom ROM users without default Google Play Services Support, this hits hard, because it basically disables them from using any apps at all, if the update from google comes irl.

Having done this, Google not only dictates you what is the source of your apps but also what OS you should have your mobile device. This is rudiculous and I will not be silent.
Internet should remain free and this is an attack on digital freedom. And this freedom is about to be violated by an enterprise for profit.
There for I gently request you
-- Go to the KeepAndroidOpen website and perform as many action from the site there as you can do.
E.g. Install F-Droid, message your local regulators and inform about the monopoly attempt, Provide feedback directly to Google using their Android developer verification requirements survey, sign the petition.
All action matters, and even if in the end it will be implemented, you should not have any remorse to yourself, because you did something towards stopping it and were not passive.
Therefore I'm requesting you, If you have the account on Google Developer Console, the best decision would be to remove it. Do not upload any IDs if you haven't yet.
Self-confession time
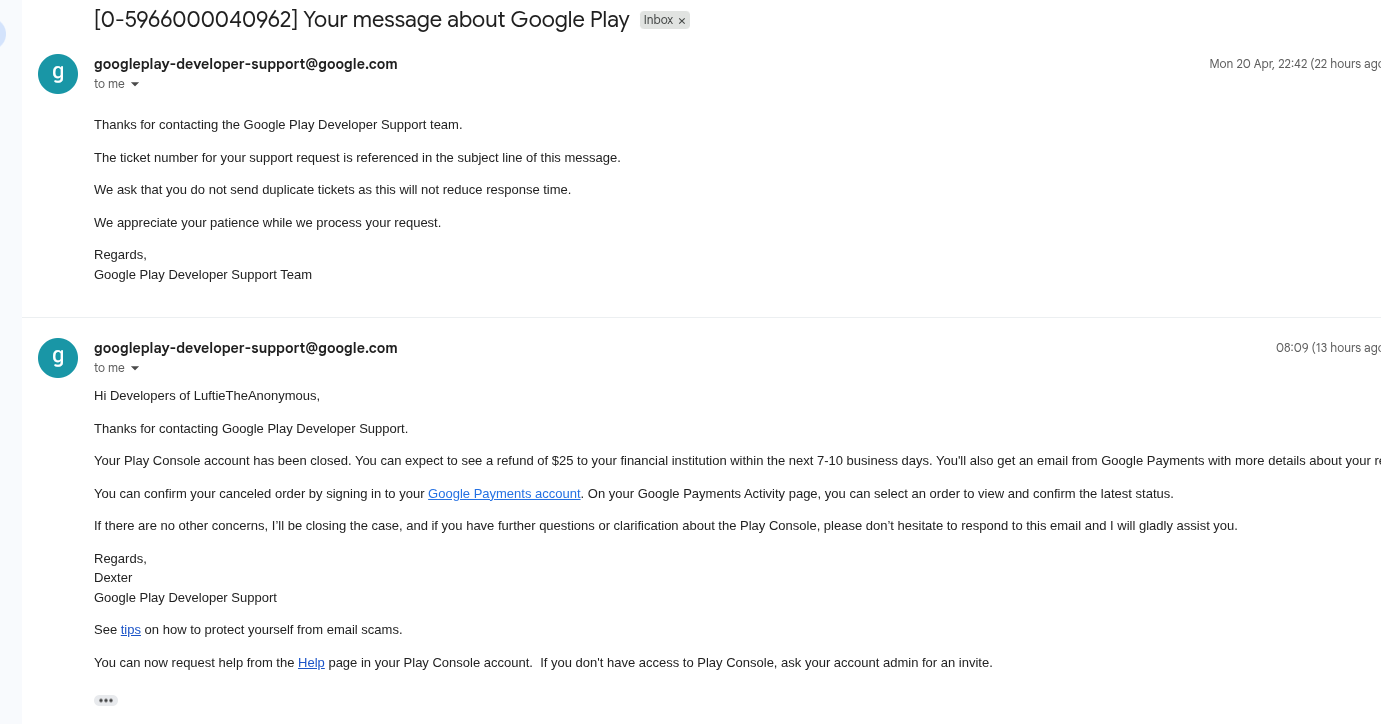
Me myself unfortunately committed back October/November 2024 a failure by uploading the sensitive data to Google, only because I was in a process of building my start-up and wanted to have a greater outreach with my app. That project has been terminated and failed, but the data remained. Thus I recently decided to remove my account from Google Play Developer Console:
Candidly speaking, when I look at how much spam I got to my gmail and how much I get to my private email addresses, 1 gmail outperforms 5 private mail addresses I have.
Spam/Scam mails quantities on my email addresses in one month:
1 Gmail: 257 mails
5 Private Mail: 0 mails
Announcement Summary
That's it from the announcement. Leave a comment down below what actions have you taken and what do you think about it, and now we can head over to the main part of the article !
Article Navigation
For those of you who want to navigate in the article, to find part they want here it is:
Messengers

Ok, until now we only discussed the Operating Systems to be used, but this is not all. You would not like your messages to be spied, misused on or be breached, right ?
Thus we need a private communicators. Me myself on a daily basis use variety of communicators, which I really do not like being completely honest. I use:
- Signal (my favorite one)
- Telegram
- SimpleX
- Matrix/Element
- Whatsapp
From those 5, only 3 are fully reliable when it comes to privacy respecting and that are:
Signal, SimpleX, Matrix
Before I discuss those 3 chat-apps, here is why I did not include Telegram and Whatsapp
Why not Telegram ?
E2EE is NOT default—standard chats are server-side encrypted, meaning Telegram can decrypt them
Custom encryption protocol (MTProto) instead of widely-audited standards like Signal Protocol
IP address leak vulnerability (MTProxy doesn't actually hide IPs as users think)
2024-2026: 200+ million records leaked via various breaches; 122GB credential archive (361M unique emails) distributed across Telegram channels in late 2023/early 2024
2024: Hackers leaked 31M+ Star Health insurance customers' medical data via Telegram bots
2025: 43.5M Telegram channels blocked for illegal activity, but actors just recreate channels within days (low cost to operate)
Why not Whatsapp ?
Meta collects metadata ruthlessly—who you message, when, how often, your contact lists
Meta monetizes this data for ad targeting
November 2025: Researchers at University of Vienna + SBA Research found 3.5 billion WhatsApp accounts via API scraping due to weak rate-limiting. They extracted profile pictures, "about" text, linked devices, OS info. One researcher: "This is a cybercriminal's dream working list."
June 2025: 16 billion credentials breach affecting Facebook/Instagram/WhatsApp (infostealer malware)
Early 2025: Graphite zero-click spyware (Paragon Solutions) targeted ~90 journalists/activists—gave attackers access to encrypted messages, microphone, location
2021: 533M Facebook accounts scraped; 58% still active on WhatsApp in 2025—leaked phone numbers have permanent value
Thus I really wish to move away from using Telegram. Unfortunately a lot of people from the crypto-industry prefer convenience and flashy effects over security and privacy.
Why the others ?
Signal

Encryption: Signal Protocol (Double Ratchet)
ECDH: Curve25519
Message encryption: AES-256-GCM
HMAC: SHA-256
Perfect Forward Secrecy: Yes (every message has unique keys)
Post-Compromise Security: Yes (ratcheting)
Architecture: Centralized servers (Signal Messenger Inc.)
Minimal data collection: No message history, no contact lists stored server-side
Registration: Phone-number based
Multi-device: Supported but uses Sesame protocol
Metadata Protection: Reasonable—server doesn't see message content, but does see phone number, online status, contact discovery
End-to-end encryption is mandatory across all chats
Open-source, regularly audited, nonprofit model
Zero metadata collection unlike WhatsApp—doesn't store who you message or call logs
Post-quantum cryptography roadmap in progress.
Before I move to the next recommendation, I have to explain couple of terms that will actually repeat themselves throughout the article.
Ratcheting - A cryptographic algorithm for dynamical updates of encryption keys to ensure forward secrecy and post-compromise security. This means that even if a key is compromised, past messages remain secure, as new keys are generated for each message exchange.
Double Ratchet - It's an key-management algorithm designed by first Signal's CEO. The feature of this algorithm is that after the initial key-exchange, it handles the ongoing renewal and maintenance of short-lived session keys.
It combines a cryptographic so-called "ratchet" based on the Diffie–Hellman key exchange and a ratchet based on a key derivation function, such as a hash-function, and is therefore called a double ratchet.
Sesame Algorithm - It's an algorithm designed for message encryption sessions management in an asynchronous across multiple devices. It is however vulnerable due to the lack of cryptographic proof of ownership. Which means that if an attacker gains access or intercepts some messages of a victim, it allows the attacker to register their device and gain access to the victim's account.
Forward Secrecy - An encryption system has the property of forward secrecy if plain-text (decrypted) inspection of the data exchange that occurs during key agreement phase of session initiation does not reveal the key that was used to encrypt the remainder of the session.
All is more nicely described by researchers from University of Luebeck.
SimpleX

Encryption: SimpleX protocol (custom, but well-designed)
Message encryption: ChaCha20-Poly1305 (AEAD)
Key encryption: XChaCha20-Poly1305 (extended nonce for random salt)
Key exchange: Curve448 ECDH
Forward Secrecy: Yes (ratcheting model similar to Signal)
Architecture: Fully decentralized—no central server required
Users run their own SMP (SimpleX Messaging Protocol) relays or use community-hosted ones
Zero-knowledge: SMP relays don't store messages; they're purely transient delivery points
No user accounts: Connections are queue-based, not identity-based—no UIDs linking users to the network
Metadata Protection: Exceptional—even relay operators can't see who's talking to whom
Tor Support: Built-in Tor integration (transport isolation per contact)
Audit: Trail of Bits security assessment (2022, 2024)
The Trade-off: SimpleX prioritizes privacy over convenience. No multi-device sync yet, no cloud backups, slower message delivery.
But this is intentional—they refuse the push-notification trap that other apps use.
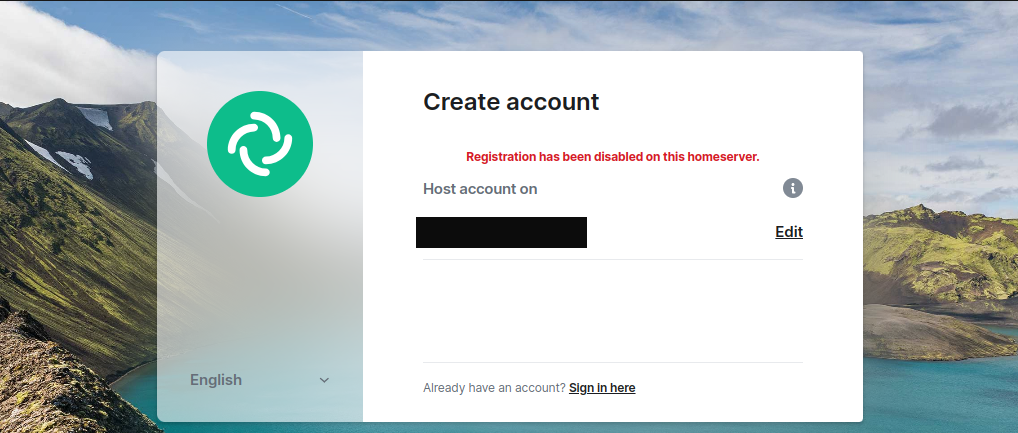
Matrix/Element
Encryption: Olm + Megolm
1-to-1: Olm (Double Ratchet variant, similar to Signal Protocol)
ECDH: Curve25519
Message encryption: AES-256-CBC (non-standard; should be GCM or
ChaCha20-Poly1305)
HMAC: SHA-256
Group chats: Megolm (sender-key model)
Session key: AES-256
Ratcheting: Weaker than 1-to-1; Forward secrecy limited by key reuse
Architecture: Federated—users can run their own home-server
Protocol is open, but implementations vary in security
Default E2EE: Yes
Key Backup Vulnerability: Server-side encrypted key backups can be exploited if home-server is malicious
Metadata: Partially exposed (room names, user IDs, member lists visible to homeserver)
Other worth-mentioning messengers
There also other emerging private messengers that are worth to be paid attention to, namely NCrypt and also Sealed. Both are blockchain focused, and the messages are stored on blockchain at least in Sealed.
Here are some information about Sealed and NCrypt I could find in their privacy policy and on the internet.
But that part will be left for the second part of the article, so stay tuned !